- Partners
- Contact Us
- Log in
VoIP Security Risks: Top Threats & How to Fix Them

Many modern businesses are turning to VoIP as it reduces communication costs and offers flexibility for teams to connect from anywhere using smartphones, desktops, or other devices.
However, since VoIP works through the internet, it also comes with security risks. Without the right protection, business calls and systems can become vulnerable to unauthorized access or service disruptions.
For this reason, businesses must understand how VoIP security works and take the right steps to protect their communication systems.
This guide explains what VoIP security risks are and offers practical ways to fix them to keep your VoIP system secure.
Key Highlights:
Businesses must secure VoIP networks because calls travel through the internet and may become vulnerable without proper protection.
Common VoIP security risks include SIP hijacking, DoS attacks, toll fraud, and malware attacks.
Security measures such as encryption, strong authentication, secure SIP protocols, and network monitoring help prevent attacks.
Regular system updates, secure internet connections, and employee awareness help maintain a safer VoIP communication environment.
What are VoIP Security Risks?
VoIP (Voice over Internet Protocol) security risks are potential threats and vulnerabilities in your VoIP phone system that can expose your data, disrupt service, or lead to financial fraud. Since this technology runs over IP networks, attackers can target your signaling protocols, user credentials, and voice data during transmission to gain unauthorized access or interrupt communication.
VoIP risks include activities such as intercepting call data, taking over user accounts, sending malicious traffic, or using the system for fraudulent calls. Each risk directly impacts how calls are initiated, routed, or transmitted within the VoIP environment.
Why VoIP Security Matters for Your Business?
VoIP security is important for businesses to protect communication channels from unauthorized access, prevent financial misuse, and avoid service disruptions. Strong VoIP security also helps protect sensitive business data from threats such as fraud and hacking.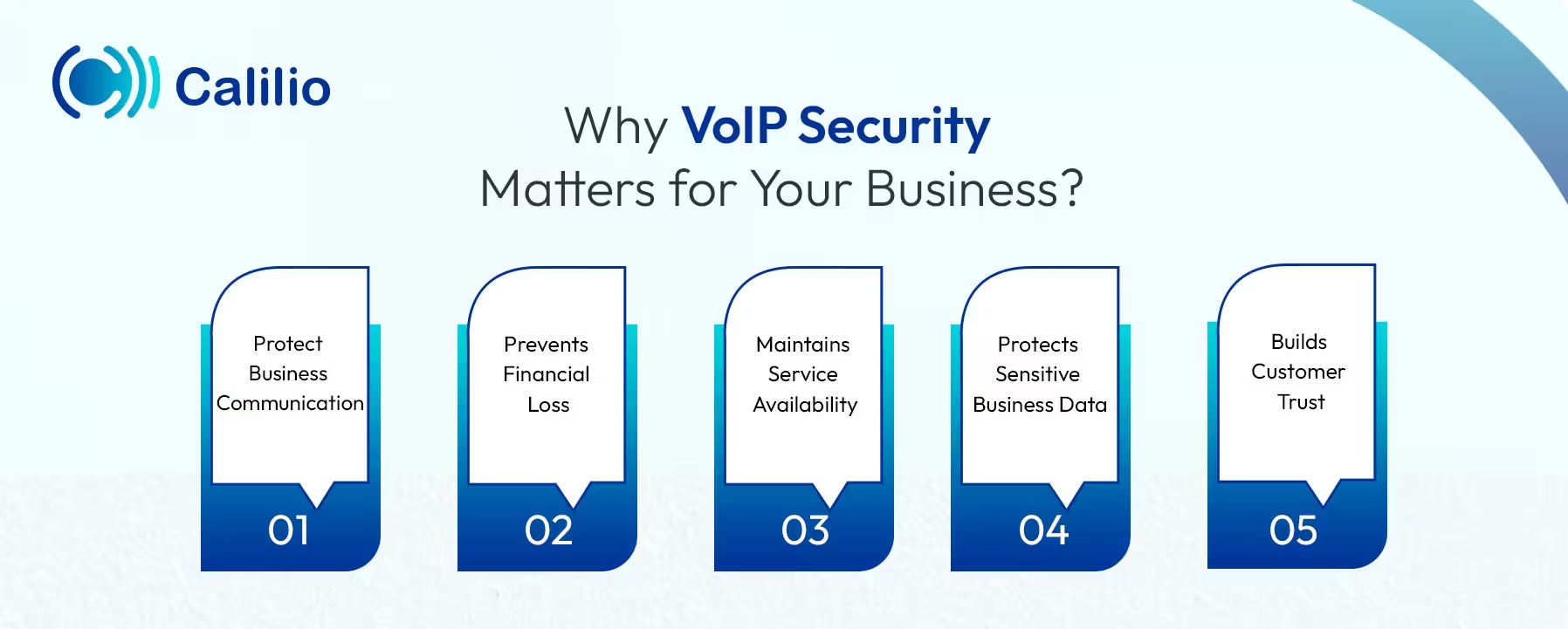
- Protect Business Communication: Businesses often discuss customer concerns, sales agreements, and internal strategies during phone calls. VoIP security helps keep these conversations protected so unauthorized users cannot access or monitor business discussions.
- Prevents Financial Loss: Attackers may exploit unsecured VoIP systems to place unauthorized calls. Strong VoIP security controls help prevent such misuse and prevent costly phone abuse.
- Maintains Service Availability: Businesses depend on phone systems for daily operations such as sales inquiries, customer support, and internal coordination. Security protection keeps the VoIP system stable and reduces the risk of disruptions that may affect sales or customer support.
- Protects Sensitive Business Data: Business calls often include customer records, order information, or payment details. VoIP security measures protect this data from interception and reduce the risk of sensitive information being exposed.
- Builds Customer Trust: When organizations secure their communication systems, they show commitment to protecting customer data and maintaining professional communication standards.
Protect Your Business Communication with Calilio’s Secure Cloud Phone System
9 VoIP Security Risks that can Affect Your Business
The most common VoIP security risks include eavesdropping, denial of service (DoS) attacks, toll fraud, SIP registration hijacking, vishing scams, malware infections, weak passwords, caller ID spoofing, man-in-the-middle attacks, and the use of unsecured Wi-Fi networks.
Understanding these risks helps your business identify vulnerabilities in VoIP networks and apply proper security measures to protect your system.
1. VoIP Eavesdropping
VoIP eavesdropping occurs when attackers intercept voice packets during transmission. If the call traffic is not encrypted, hackers may capture conversations and gain access to sensitive information such as customer data, business discussions, or authentication details.
2. Denial of Service (DoS) Attacks
A Denial of Service (DoS) attack overwhelms your VoIP server with excessive traffic by sending too many requests at once. This overload prevents the actual customer calls from reaching you. Such disruptions can affect customer support, sales communication, and internal coordination.
3. Toll Fraud
Toll fraud occurs when unauthorized users gain access to a VoIP system and use it to make outgoing calls to international or premium-rate numbers. This can lead to high telecom charges, disrupt telecom expense management, and cause financial loss for your business.
4. VoIP Phishing
VoIP phishing, also known as voice phishing, is a phone scam where attackers use VoIP systems to make fraudulent calls. Attackers impersonate trusted organizations such as banks, service providers, or government agencies to persuade individuals to reveal sensitive information like account credentials or payment details.
5. Malware Attacks
Devices connected to a VoIP network, such as computers or IP phones, can become infected with malware. Once malware enters the system, it may monitor communication, steal information, or allow attackers to remotely control your devices.
6. Voicemail Hacking
Voicemail in VoIP systems can be vulnerable when businesses use weak PINs, default passwords, or unsecured remote access settings. If attackers gain access, they can listen to private messages, change greetings or system settings, and use the voicemail account to collect sensitive business information or mislead callers.
7. Man-in-the-Middle Attacks
In a Man-in-the-Middle (MitM) attack, hackers secretly intercept communication between two VoIP users. They position themselves within the network path and capture or modify call data without the participants noticing.
8. War Dialing
War dialing is a technique where attackers use automated tools to dial a large range of phone numbers to find active VoIP lines, extensions, or voicemail systems. Once they identify the vulnerable systems, they try to access them using default credentials or weak security settings, which can lead to unauthorized system access and further attacks.
9. SIP Registration Hijacking
In Session Initiation Protocol (SIP) registration hijacking, an attacker registers their own device to your system using a legitimate user’s SIP credentials, which allows them to take over that extension. Once they take control of the account, they may redirect incoming calls, impersonate the user, or place fraudulent calls through your system.
How to Fix VoIP Security Risks?
To fix VoIP security risks, combine strong access control, secure configurations, and continuous monitoring. Always use strong passwords and authentication, enable call encryption, secure SIP settings, deploy firewalls and session border controllers, and keep systems updated to reduce vulnerabilities.
1. Use Strong Passwords and Authentication
Create strong and unique passwords for every VoIP account and device by combining uppercase and lowercase letters, numbers, and special characters. Also, enable Multi-Factor Authentication (MFA) so users must verify their identity through an additional step before accessing the system. This will help to reduce the risk of unauthorized access.
2. Enable Call Encryption
Protect voice data by enabling encryption. Use protocols such as Secure Real-time Transport Protocol (SRTP) to encrypt call audio and Transport Layer Security (TLS) to secure call signaling. Encryption ensures that only authorized users can access the call data during transmission.
3. Secure SIP Configuration
Configure SIP settings carefully. Restrict unverified registrations, enable strong SIP authentication, and allow access only from trusted devices or IP addresses. Proper SIP security prevents attackers from hijacking user accounts or redirecting calls.
4. Deploy Firewalls and Session Border Controllers
Install network firewalls and Session Border Controllers (SBCs) to protect the VoIP infrastructure. These tools inspect incoming and outgoing traffic, block suspicious requests, and help defend the system from external attacks such as DoS attempts.
5. Keep VoIP Systems Updated
Update VoIP software, IP phones, and related applications regularly. Security updates fix known vulnerabilities and strengthen system protection against emerging threats.
6. Monitor Call Activity and System Logs
Track call records and system activity to detect unusual behavior. For example, unexpected international calls or abnormal call volumes may indicate unauthorized system access. Early detection helps businesses respond quickly and prevent further misuse.
7. Use Secure and Reliable Networks
Operate VoIP systems on protected business networks. Avoid connecting VoIP devices to unsecured public Wi-Fi because attackers can monitor network traffic and attempt to intercept call data.
What are the Best Practices to Improve VoIP Security?
You can improve your VoIP security by implementing strong operational practices such as conducting regular security audits, separating VoIP networks from other systems, and educating employees about communication-related threats.
Conduct Regular Security Audits
Review VoIP systems, network configurations, and access settings regularly. These audits help identify potential security gaps early, so your business can correct issues before they affect communication systems.
Promote Employee Security Awareness
Train employees to recognize threats such as vishing attempts, caller ID spoofing, and suspicious requests for sensitive information. When staff understand these risks, they can respond carefully and report unusual activity quickly.
Network Segmentation
Separate VoIP traffic from other business networks using a dedicated network segment or Virtual Local Area Network (VLAN). It limits system exposure and helps stop attackers from spreading to other parts of your network if one area gets compromised.
Wrapping Up
Securing your VoIP system is vital to protect business communication and sensitive data. Without proper safeguards, VoIP risks such as fraud, call disruption, and data exposure can compromise privacy, disrupt services, or lead to financial loss.
By using strong security measures like encryption, secure configurations, and regular monitoring, businesses can reduce these risks. Building a security-focused work culture and choosing a reliable VoIP provider further helps limit vulnerabilities and keeps communication stable.
In particular, Calilio, a cloud-based VoIP solution, offers end-to-end encryption, call analytics, and activity monitoring to help detect unusual patterns and maintain control over your communication system. We help you make the most of the VoIP technology without worrying about security issues.
Summarize this blog with:
Frequently Asked Questions
Is VoIP secure for business communication?
Yes, VoIP is secure for business communication when organizations implement proper security controls. Most VoIP service providers include features like encrypted voice transmission, controlled access, secured SIP settings and network protections to protect systems from potential threats.
What is the biggest VoIP security risk?
How can businesses protect their VoIP systems?
Can VoIP calls be hacked?

Still have questions?
Can’t find the answer you’re looking for? Please chat with our friendly team.
Stay in the loop
Get the latest call insights, trends, and updates delivered straight to your inbox.
By subscribing, you agree to receive updates from Calilio.
You can unsubscribe anytime.
Enter the World of AI Business Phone System with Calilio
Improve your business operation with Calilio's advanced virtual phone system. Join today for a better way to connect.
